
The Evolving Role of CISOs: Top Priorities in 2025
March 20, 2025, CISO
Today, CISOs stand at a critical intersection of technology, business strategy, risk management, and human… Read More
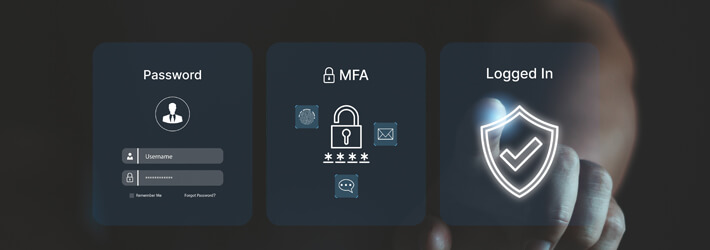
What is Multi-Factor Authentication (MFA) and How does It Work?
February 11, 2025, General
56% of survey respondents supported SMS Time Based One-Time Passwords (TOTPs), and 51% supported email… Read More

Australian Privacy Act Overview
April 25, 2024, Compliance
In response to a series of high-profile data breaches, the Australian government implemented significant reforms… Read More

Authentication vs Authorization: Difference Between Authentication and Authorization
February 13, 2024, Data Security
Authentication and authorization are two indispensable processes that safeguard systems and data. Authentication performs the… Read More

What is the Principle of Least Privilege (PoLP)? The Principle of Least Privilege (PoLP) is… Read More

What is Sensitive Data? Examples, and Types
December 18, 2023, Data Security
Data has become one of the most valuable assets for organizations, hence why it is… Read More


