Last Updated on January 17, 2025 by Satyendra

Knowing how to detect ransomware is more critical now than ever before.
Ransomware attacks are on the rise. According to recent research, the number of ransomware attacks nearly doubled in the first half of 2021, with the United States being the most targeted country – accounting for roughly 55% of infections.
What is Ransomware and How Does it Work?
Ransomware is a form of malware that encrypts the victim’s data and holds it to ransom. Once the victim’s data has been encrypted, they will be presented with a message informing them that they must pay a ransom, usually in Bitcoin, in order to get access to the decryption key. Recent strains of ransomware use the “double extortion” technique, which involves taking a copy of the victim’s data before initiating the encryption process. The attackers will then threaten to expose the data to the public if the victim refuses to pay the ransom.
Common Ransomware Attacks
The majority of ransomware attacks arrive via email, via some kind of social engineering technique, such as Phishing. The attacker will usually masquerade as a trusted entity in order to trick the victim into downloading a malicious application.
However, there are numerous other ways that infections can happen. For example, in some cases, the victim will be redirected to a malicious website, which prompts them to install the ransomware program. Alternatively, the website may present a fake login screen, which the attacker will use to harvest credentials, and then use those credentials to launch an attack from within the target organization.
Some forms of ransomware are embedded within applications and plug-ins, which the victims install believing them to be trusted. Although less common, there are cases where the ransomware program is stored on a removable drive, which will automatically execute when the victim connects the drive to their device. We are also starting to see an increase in the number of ransomware attacks that use Remote Desktop Protocol (RDP) to execute the script.
Signs of a Ransomware Attack
It takes an estimated forty-three minutes for the average ransomware variant to encrypt 100,000 files. Naturally, different companies will store a different number of files, and so it is difficult to accurately predict how long it will take for a ransomware attack to fully unfold. However, assuming that companies have the right solutions in place, even a small time-window can be enough to stop an attack in its tracks. Of course, in order to prevent a ransomware attack from spreading, there are signs that you will need to look out for, which include;
- A spike in disk activity, as the ransomware script searches for, and encrypts the files on your system.
- Poor system performance, as the script uses up system resources to perform searches and encrypt the files.
- The creation of new accounts, especially privileged accounts.
- Suspicious inbound and outbound network traffic, as the ransomware script communicates with the Command & Control (C&C) Server.
- The installation of unauthorized software, as attackers install various tools, such as Mimikatz, to help them exploit vulnerabilities, and carry out other relevant tasks.
- Security systems are being tampered with, in an attempt to thwart monitoring activities.
- Backups are being tampered with, in an attempt to prevent the victim from restoring their files.
- Ports are being scanned inside your network, thus suggesting that the attackers are trying to move laterally from one system to another.
- Applications are no longer working, as the files, they depend on are being encrypted.
Why You Need Early Ransomware Detection
Naturally, the earlier you identify any type of cyber-attack, the better your chances of preventing it or at least stopping the attack from spreading.
This is especially true for Ransomware, as the damage that can be caused by a ransomware attack can be irreversible.
After all, even if the victim pays the ransom, there’s no guarantee that they will give you the decryption key, and if they extracted copies of your data before initiating the attack, you will never know what they will do with those copies.
In short, the faster you are able to respond to a ransomware attack, the less chance the attacker will have to steal your sensitive data and disrupt your systems.
Common Challenges in Ransomware Detection
One of the reasons why ransomware attacks are successful is because they can penetrate your network via a large number of end-points, and then execute in a covert manner. Below are the most common challenges associated with ransomware detection.
Employees are the weakest link
As with most forms of malware, ransomware attacks typically arrive via some form of social engineering technique, and in most cases, organizations only become aware of the attack once all data has been encrypted. The problem with detecting social engineering attacks is that they are inherently deceitful and tend to prey on unsuspecting victims.
Ransomware attacks spread very quickly
Once the targeted organization has been infected, the ransomware script will try to propagate to as many different systems as possible, thus making it very difficult to contain.
Some strains don’t leave a trace
Over the last five years we’ve seen a proliferation of strains known as “file-less ransomware”, which are even harder to detect than other strains as they do not install any files on the victim’s device. File-less ransomware attacks usually take advantage of Microsoft Windows PowerShell, which gives adversaries access to pretty much everything and anything in a Windows environment.
Common Ransomware Detection Techniques
Most companies will already utilize software solutions such as anti-virus software, SPAM filters, and sandboxes. However, these days, many strains of ransomware are able to evade such solutions. While there may not be a ‘magic bullet’ when it comes to detecting and preventing ransomware attacks, there are some best practices that organizations should adhere to, which include:
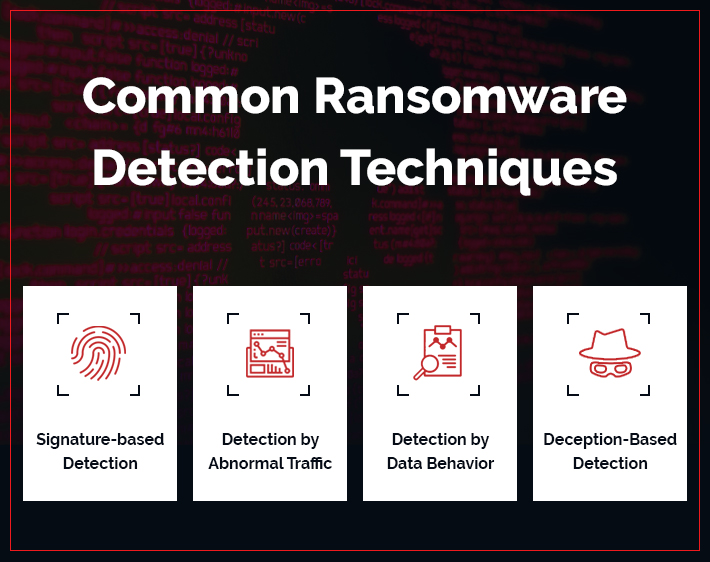
Signature-based Detection or Detection by Signature
Signature-based ransomware detection is a method of detecting ransomware by comparing ransomware binary hashes to known signatures, enabling a fast analysis of files. Security platforms and antivirus software capture data from executables to determine whether they are ransomware or approved executables. Although signature-based ransomware detection is a valuable first layer of defense, it is not able to identify new ransomware strains, as attackers frequently modify malware files to evade detection. Simply adding one byte to a file creates a new hash and decreases the likelihood of malware detection. As such, signature-based detection assists in identifying older ransomware strains, but more advanced, targeted ransomware campaigns can bypass this form of detection.
Detection Based on Data Traffic or Detection by Abnormal Traffic
It is also possible to detect ransomware by analyzing network traffic, which involves examining the information that is transferred between endpoints. This method will check for things like time stamps and data volumes, and any irregularities that might be a sign of a ransomware attack. If suspicious activity is detected, the system will be locked down. One advantage of this method is its ability to prevent ransomware attacks without requiring knowledge of the malware signature. However, this method has a tendency to produce false positives resulting in legitimate files being blocked, negatively impacting productivity and resulting in costly downtime.
Detection by Data Behavior
Ransomware typically encrypts or locks files before demanding payment for decryption. Therefore, monitoring unexpected changes in file storage locations or sudden spikes in file encryption activity can reveal signs of a ransomware attack. In contrast to signature and data traffic methods, no signature is required for this method, meaning there are fewer false alarms. Additionally, it doesn’t entail locking down the whole file system; instead, suspect processes can be hindered. This approach won’t actually prevent a ransomware infection, but will instead help to prevent the attack from spreading once it has been identified. There are numerous data security platforms that offer a “threshold alerting” feature, which is able to detect and respond to events that match a pre-defined threshold condition. For example, if multiple files are encrypted or renamed within a given time-frame, a custom script can be automatically executed in response to the potential threat.
Deception-Based Detection
Cyber-deception technology can be used to redirect ransomware to fake files by creating a pseudo network with attractive decoys that are indistinguishable from the legitimate network. It does not require any network changes or installing agents on endpoints. Deception technology helps in identifying the attacker’s infiltration methods, which might include taking advantage of weak passwords or compromised endpoints/servers, which can then be secured to prevent further attacks. The first step in implementing deception solutions involves creating a fake shared drive that is distributed throughout all endpoints and servers in the network. This fake network is concealed from legitimate users to prevent them from accidentally triggering alerts. An effective cyber-deception tool should be able to integrate with third-party security tools like IPS solutions, firewalls, and next-gen AV in order to quickly identify malicious activity. As soon as ransomware infects an endpoint and initiates the encryption process, the decoy will slow down the encryption process and isolate the threat. It can also integrate with existing security solutions to contain the threat.
Related Articles:
How Lepide Helps in Ransomware Detection
The Lepide Data Security Platform can help to secure your accounts and data – before, during, and after a ransomware attack. To start with, you need to ensure that regular users only have access to the data they need to perform their role.
If access controls are assigned responsibly, were an employee to fall victim to a phishing attack and install the ransomware application, it would only be able to encrypt a relatively small number of files.
The Lepide Data Security Platform will help you discover and classify your critical assets, thus making it easier to assign the appropriate access controls. It will also help you identify which regular users have access to sensitive data.
Once an attack has been initiated, Lepide can help you prevent the attack from spreading by automating a response to events that match a pre-defined threshold condition, such as when an unusually large number of files are being copied to an external server, or encrypted within a given time-frame.
As mentioned above, a custom script can be executed to perform a number of operations that can help to stop the attack in its tracks. It’s also a good idea to use a real-time auditing solution to detect and respond to changes made to your backups (assuming they are stored on the same system), as changes to backups may suggest that an attacker is trying to delete or encrypt them.
You will also need to keep track of any newly created accounts, as attackers often try to use new accounts in order to operate in a stealthy manner.
Following a ransomware attack, you will need to carry out a forensic analysis of the events that took place prior to the attack, to ensure that you are able to prevent the attack from reoccurring and to ensure that the attacker no longer has access to your network.
In addition to closely monitoring privileged accounts, the Lepide Data Security Platform will provide a summary of all events that took place prior to the incident, via a single dashboard, with various options for sorting and searching.
If you’d like to see how the Lepide Data Security Platform can help you detect ransomware attacks, schedule a demo with one of our engineers.


 Group Policy Examples and Settings for Effective Administration
Group Policy Examples and Settings for Effective Administration 15 Most Common Types of Cyber Attack and How to Prevent Them
15 Most Common Types of Cyber Attack and How to Prevent Them Why AD Account Keeps Getting Locked Out Frequently and How to Resolve It
Why AD Account Keeps Getting Locked Out Frequently and How to Resolve It
