Last Updated on April 2, 2025 by Satyendra

For businesses of all sizes, protecting and managing network resources is crucial in today’s linked digital environment. A key component of this task is the idea of a domain controller, a specialized server in charge of user and device authentication and authorization within a network domain. Domain controllers guarantee that only authorized users can access particular resources by centralizing user credentials and enforcing security policies, protecting the network’s integrity and security.
What is a Domain Controller (DC)?
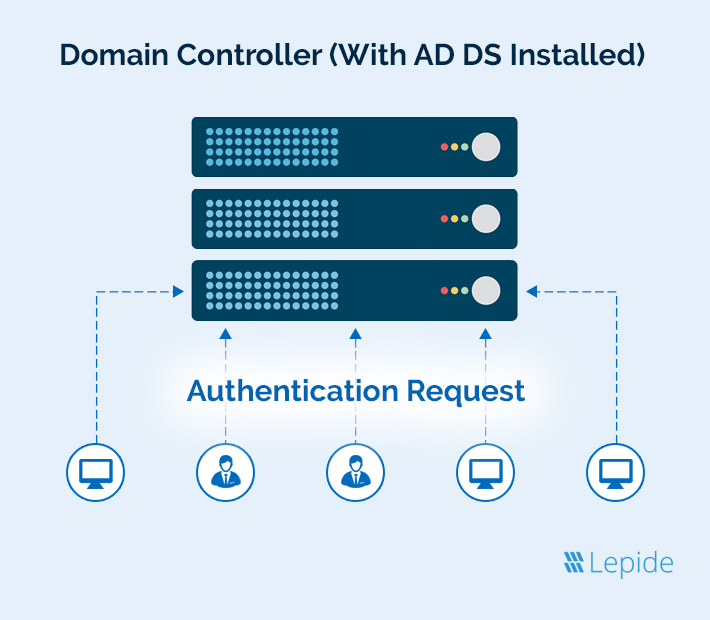
The server in charge of handling requests for network and identity security is known as a domain controller (DC). It serves as a gatekeeper, verifying that the user is permitted to access the domain’s IT resources. More precisely, a domain controller is a computer that has Active Directory Domain Services (AD DS) installed and runs the Windows Server operating system. DCs cannot be desktop computers, laptops, or other devices running a standard version of Windows.
There must be a minimum of one domain controller per Active Directory (AD) domain. Any modifications made to the directory file are duplicated to all other DCs within the domain, and each DC keeps a copy of the file. In addition to providing essential services like permissions and authentication, all domain controllers have specific roles that allow them to carry out other tasks.
How Domain Controller Works?
Domain controllers are primarily responsible for determining and validating user access to a network by authenticating and validating users, including group policies, user credentials, and computer names. In addition to offering Active Directory services like permissions and authentication, each Domain Controller in a domain keeps a copy of the directory. Ntds.dit is a directory file that holds information on computers, users, security groups, and other items in that domain. It also contains details about the Active Directory schema, which lists every type of object that may be kept in the directory. procedures, and so forth.
To keep everyone in the domain up to date, any changes made to the copy of the directory on one DC, for example, when a user changes their password or their account is locked out due to too many wrong password attempts is duplicated to the other DCs in the domain so they remain up to date. It should be noted that Active Directory domain controllers offer authentication and authorization services for machines, apps, processes, and more, in addition to user accounts.
Download 20-Day Free Trial
What are the Advantages of Domain Controllers
- Managing AD Admin Rights: The domain controller manages Active Directory administrative privileges and restricts domain user accounts by verifying the authorization of each computer connected to the network before granting access to sensitive files. It evaluates user accounts to assign administrative privileges and access rights solely to individuals necessary for their job functions. Additionally, the domain controller enforces the use of strong passwords to protect user accounts.
- Resource Sharing: Domain controllers facilitate centralized resource sharing by connecting all devices within a network. Administrators can assign user-specific access permissions, allowing authorized individuals to access various computers and devices. This centralized management reduces the need for additional hardware purchases, such as printers and computers, leading to cost savings.
- Prevention of Unauthorized Access: Domain controllers implement security measures to prevent unauthorized network access. They can lock user accounts after multiple failed login attempts, immediately disable accounts when an employee leaves the organization, require credentials for unlocking screens, and restrict USB access based on user permissions and access rights.
- Cost-Efficient and Time Saving: Managing and configuring each device individually can be time-consuming and inefficient. Implementing a domain controller streamlines this process by allowing administrators to set login credentials and security settings from a centralized server, thereby saving both time and costs. Additionally, domain controllers facilitate the automatic installation of network printers when devices join the domain, enabling centralized management tasks such as pausing, commanding, or restarting printing devices across the network.
- Enhances Security Posture: A Domain Controller (DC), which enforces strong password restrictions throughout the network, is essential to improving an organization’s security posture. By centralizing authorization and authentication procedures, the DC reduces the danger of weak passwords, which are a common entry point for data breaches, and guarantees that all user accounts follow established security guidelines.
What are the Disadvantages of Domain Controllers?
- Complex Configuration and Maintenance: A domain controller requires considerable planning and knowledge to set up and maintain. Unauthorized access, data breaches, or network outages can result from misconfigurations. To guarantee optimum security and performance, regular maintenance is required.
- Single Point of Failure: If a single domain controller is used, the authentication and authorization procedures throughout the entire network may be affected if it is rendered inoperable by hardware malfunction, cyberattacks, or other problems.
- Security Vulnerabilities: Domain controllers are major targets for cyberattacks since they serve as central repositories for user credentials and consents. If compromised, attackers may be able to access sensitive information and vital systems by gaining enhanced privileges.
- Dependency on Uptime: The network’s operations are heavily dependent on the continuous availability of the domain controller. Any periods of inactivity or downtime can result in authentication challenges, hindering users from accessing essential network resources.
What is the Difference Between a Domain Controller and Active Directory?
The domain controller is the server that contains the Active Directory service and is in charge of user and computer authentication and authorization inside a domain. It ensures that only authorized users may access particular resources, maintains user credentials, and enforces security standards. The DC essentially serves as the gatekeeper, verifying login requests and granting access based on the data that is kept in the Active Directory.
Microsoft created the directory service known as Active Directory, that contains data on network objects such as computers, printers, users, and groups. Within a Windows domain network, it offers centralized management and authentication in addition to organizing this data in a hierarchy. AD gives administrators the ability to effectively control network resource access and permissions.
While the domain controller operates as the server that runs the Active Directory service, managing authentication and enforcing security policies inside the domain, Active Directory is the comprehensive database and directory service that stores and arranges information about network resources. Managing identities and links between separate resources is made easier with the structure of Active Directory. By processing authentication requests and implementing policies, the Domain Controller, on the other hand, carries out the services specified by Active Directory.
Why is Domain Controller Security Important?
Domain controllers play a pivotal role in network security by managing user authentication and access to domain resources. They enforce security policies, such as password requirements and account lockout procedures, to ensure that only authorized users can access specific resources. Given their central role, domain controllers are prime targets for cyberattacks; unauthorized access to a DC can compromise the entire network’s security.
Domain controllers safeguard network resources by ensuring that only authorized users can access them, managing and authenticating local domain identities through directory services. They are designed to scale, accommodating the needs of large and complex networks with customized directory requirements.
Enhancing the security of a domain controller is essential to protect an organization’s network infrastructure. Key measures include:
- Implementing Firewalls
- Network Segmentation
- Restricting Insecure Protocols
- Ensuring Physical Security
How are Domain Controllers Setup in Active Directory?
Domain controllers can be installed on real servers, operating as cloud directory services, or as virtual machines (VMs). Each domain controller should be installed on a separate server as a recommended practice. One example of this is virtual domain controllers, which ought to operate on virtual machines operating on various physical hosts. The domain controller is less likely to be impacted by a compromise on another computer as a result.
The following procedures are involved in configuring an AD domain controller:
- Evaluation of the Domain: Evaluating the domain in which a domain controller will be installed is the first step in the process. Identifying the kinds of domain controllers required, their locations, and their compatibility with the domain’s current systems are all part of this evaluation.
- Integrated Domains: When planning to deploy new Active Directory (AD) domain controllers or integrating additional controllers into an existing domain, it’s essential to assess the optimal placement for the domain controller and evaluate the resources required to support both centralized and virtual domain controllers.
- Security For Threats: Designing a secure domain controller architecture is crucial to protect against both internal and external threats. The system should be resilient to service disruptions, including connectivity losses, power outages, and system failures, ensuring continuous and reliable network operations.
Other Domain Controller Implementation Options
When configuring a domain controller with Active Directory, several options are available to tailor its functionality to your organization’s needs:
- Domain Name System (DNS) Server: The domain controller can be set up to function as a DNS server, facilitating the translation of computer names to their corresponding Internet Protocol (IP) addresses.
- Global Catalog Capabilities: Enabling the global catalog allows the domain controller to retrieve Active Directory information about any object within the organization’s forest, irrespective of the object’s domain. This feature is particularly beneficial for large enterprises with multiple AD domains.
- Read-Only Domain Controller (RODC): In scenarios such as branch offices or locations with limited network connectivity, the domain controller can be configured as read-only, enhancing security and reducing replication traffic.
- Directory Services Restore Mode (DSRM): This mode facilitates emergency maintenance tasks, including restoring backups on the domain controller. It’s essential to set a DSRM password during configuration to ensure access when needed.
- Certificate Services: By enabling certificate services, the domain controller can issue and authenticate certificates used for authentication and encryption purposes within the network.
- Group Policy Hosting: Domain controllers host Active Directory group policies, which can be utilized to enforce security settings across domain member servers and client machines, ensuring consistent policy application.
- Distributed File System (DFS): Implementing DFS allows multiple file servers to host shared files, with automatic replication and an abstraction of the underlying server structure from end-users, enhancing data availability and redundancy.
Selecting and configuring these options appropriately ensures that the domain controller aligns with organizational requirements, promoting a secure and efficient network environment.
Domain Controller Setup Best Practices
Implementing robust security measures for your Active Directory (AD) environment is essential to protect organizational assets and ensure compliance. Key practices include
Principle of Least Privilege: The Principle of Least Privilege (PoLP) is a fundamental cybersecurity guideline that dictates granting users, applications, and systems only the access rights essential for their specific duties. Implementing PoLP is particularly crucial for Domain Controllers, as it minimizes the risk of unauthorized access and potential data breaches. Regularly reviewing and adjusting permissions ensures that access levels remain appropriate to users’ roles, thereby enhancing the overall security of the network.
Implement Real-Time Auditing and Alerts: Implementing real-time auditing and alerts is crucial for maintaining the security and integrity of your network’s domain controllers. By continuously monitoring and promptly reporting unusual or excessive login attempts, you can detect and respond to potential security incidents effectively. Equipping your domain controllers with comprehensive auditing and alerting capabilities not only enhances your organization’s security posture but also aids in compliance with standards like SOX, HIPAA, and PCI.
Regular Data Backup and Recovery: Regular data backup and recovery are essential practices for safeguarding an organization’s information assets and ensuring business continuity. Implementing a consistent backup schedule involves creating duplicate copies of critical data at predetermined intervals, which can be stored on-site, off-site, or in cloud-based solutions. This strategy protects against data loss due to hardware failures, cyberattacks, human errors, or natural disasters.
Centralize and Automate Management: Centralizing and automating management processes involve integrating various administrative functions such as reporting, reviews, and user controls into a single, unified system. This consolidation enhances efficiency by providing a clear chain of command and consistent communication across the organization. By maintaining all data in a single system, organizations reduce redundancy and improve accuracy, ensuring that decisions are based on reliable information.
Standardize Domain Controller Configurations: Maintain consistent and secure configurations across all domain controllers. Use deployment and configuration management tools to capture and enforce security settings, boot configurations, and hardware setups, reducing vulnerabilities and enhancing security.
Regularly Patch and Address Vulnerabilities: Establish efficient patch management processes to identify and remediate security weaknesses promptly. Keeping systems updated is crucial to protect against exploits and maintain the integrity of your Active Directory environment.
By implementing these practices, organizations can strengthen their Active Directory security posture, safeguard sensitive information, and ensure compliance with regulatory requirements.
How Does Lepide Help?
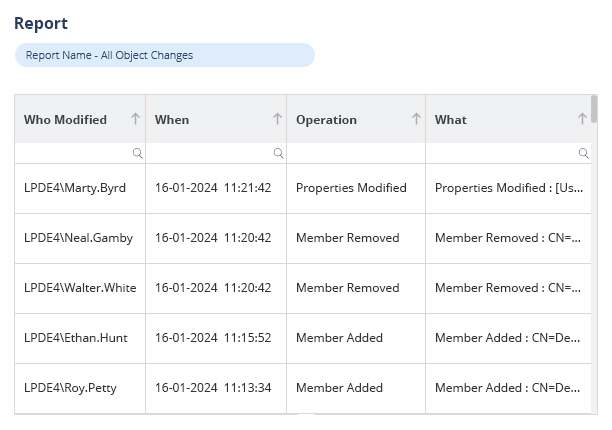
Lepide Active Directory Auditor offers a user-friendly solution for monitoring and auditing changes within Active Directory. It provides detailed reports on modifications, including those to Group Policy and security group memberships, enabling administrators to track alterations effectively. The tool’s threshold alerting feature detects suspicious activities by generating alerts when specific conditions are met, such as multiple account lockouts within a short period. This proactive approach aids in identifying potential security threats and facilitates automated responses to mitigate risks.
Given the critical role of the Domain Controller as the central hub of an Active Directory domain, safeguarding it is paramount. A compromised Domain Controller can have devastating effects on an organization. Implementing robust security measures, including the use of comprehensive auditing tools like Lepide Active Directory Auditor, is essential to monitor changes, enforce security policies, and protect against unauthorized access.
Strengthen your network security with our Domain Controller solutions. Schedule a demo or download a Free Trial today to discover how Lepide can safeguard your infrastructure.

 Group Policy Examples and Settings for Effective Administration
Group Policy Examples and Settings for Effective Administration 15 Most Common Types of Cyber Attack and How to Prevent Them
15 Most Common Types of Cyber Attack and How to Prevent Them Why AD Account Keeps Getting Locked Out Frequently and How to Resolve It
Why AD Account Keeps Getting Locked Out Frequently and How to Resolve It
