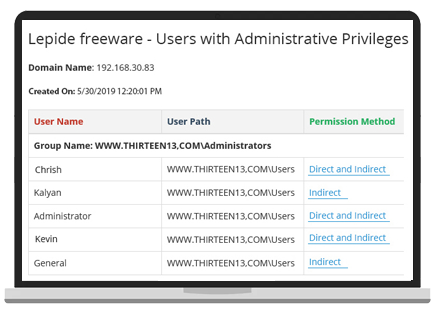
Lepide Auditor
Windows File Server Auditing Software
The easiest, yet most comprehensive way to audit file server changes and data access, track interactions with data and detect threats.
Fill in the rest of the form to
download the 20-day free trial
download the 20-day free trial
x